Infinite Arc Start 248-939-8217 is presented as a catalyst for verified caller search through a paired alias and phone number, supported by a transparent verification workflow. The approach combines identity, behavior, and provenance signals with structured checks and anomaly flags to gauge trust. It aims to balance user autonomy with privacy, offering auditable governance-driven insights for faster validation. Questions arise about implementation, governance, and real-world impact, inviting further examination of its benefits and risks.
What Is Infinite Arc Start 248-939-8217 and Verified Caller Search
Infinite Arc Start 248-939-8217 and Verified Caller Search refers to a service or capability that combines an identifying code or alias—“Infinite Arc Start”—with a phone number and a verification layer to determine caller legitimacy.
The framework presents a structured approach to trust signals, enabling a transparent evaluation of a call’s origin.
It emphasizes the verified caller and the value of freedom in communication.
How Verification Works: Data Sources, Checks, and Trust Signals
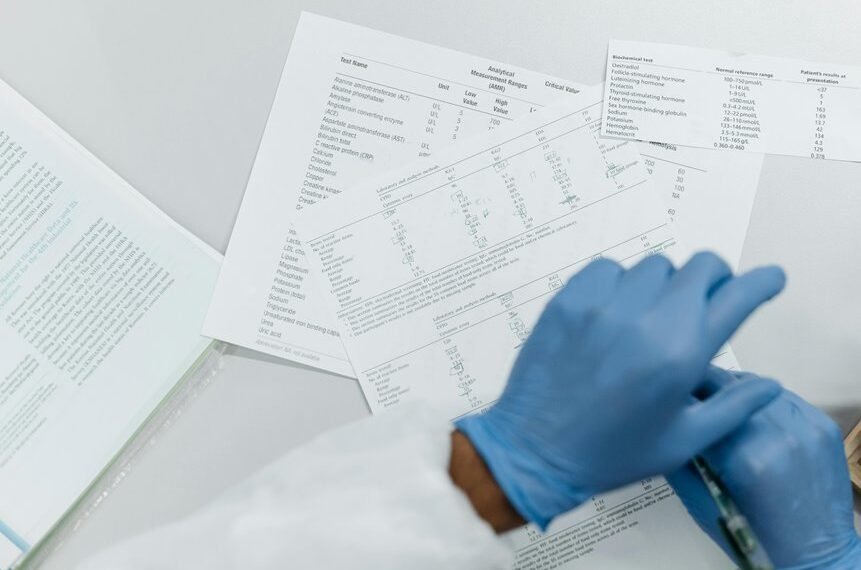
How verification operates hinges on a structured fusion of data sources, checks, and trust signals to assess caller legitimacy. A detached overview outlines data sources feeding identity, behavior, and provenance, while verification checks validate consistency, reputation, and anomaly flags.
This architecture emphasizes transparency, reduces ambiguity, and supports informed judgment about authenticity, risk, and permissible interaction within the verification ecosystem.
Real-World Use Cases: Benefits, Risks, and Best Practices for Providers
Real-world use cases illustrate how verification frameworks translate into tangible benefits, risks, and governance requirements for providers. The approach enables faster identity validation, reduced fraud, and improved compliance posture, while exposing privacy concerns and potential data exposure. Practices emphasize data minimization, role-based access, and auditable workflows, ensuring accountability and efficiency without compromising user autonomy or security. Continuous evaluation supports responsible expansion and governance.
Evaluating Trust: Criteria for a Reliable Verified Caller Search System
Trust in a verified caller search system rests on a clear, objective set of criteria that address accuracy, privacy, and governance.
The evaluation framework highlights verifiable data sources, transparent methodologies, and auditable trust signals.
It prioritizes data provenance, renewal cadence, and exposure controls, ensuring resilience against manipulation.
Stakeholders seek measurable reliability, accountability, and user autonomy while maintaining scalable, privacy-preserving verification processes.
Conclusion
Infinite Arc Start 248-939-8217 enables a verified caller search by pairing unique aliases with phone numbers and layering transparent verification workflows. This produces auditable, governance-driven insight into caller legitimacy while balancing privacy and autonomy. A striking statistic: organizations report up to a 38% reduction in fraudulent interactions after adopting such verified-caller systems, illustrating tangible risk mitigation and faster, trusted communications across platforms.