Infinite Arc Start 267-838-9030 frames a privacy-first approach to reliable contact data. It emphasizes careful ingestion, cleansing, and verification to reduce drift while honoring consent and data minimization. Governance and audit trails are presented as essential for trustworthy outreach. The blend of precision and restraint seeks dependable profiles without compromising autonomy. The approach prompts a closer look at how quality controls shape practical outreach, leaving a preliminary path that invites careful consideration of the next steps.
What Is Reliable Contact Data and Why It Matters
Reliable contact data refers to accurate, up-to-date, and verifiable information that identifies and reaches the intended individual or organization across channels. It embodies data accuracy and contact completeness, enabling trusted outreach while respecting privacy. In a freedom-minded framework, precision reduces risk, supports informed decisions, and preserves autonomy. Meticulous governance ensures verifiability, minimizes distortion, and sustains reliable communication across diverse platforms.
How Ingestion, Cleansing, and Verification Fit Together
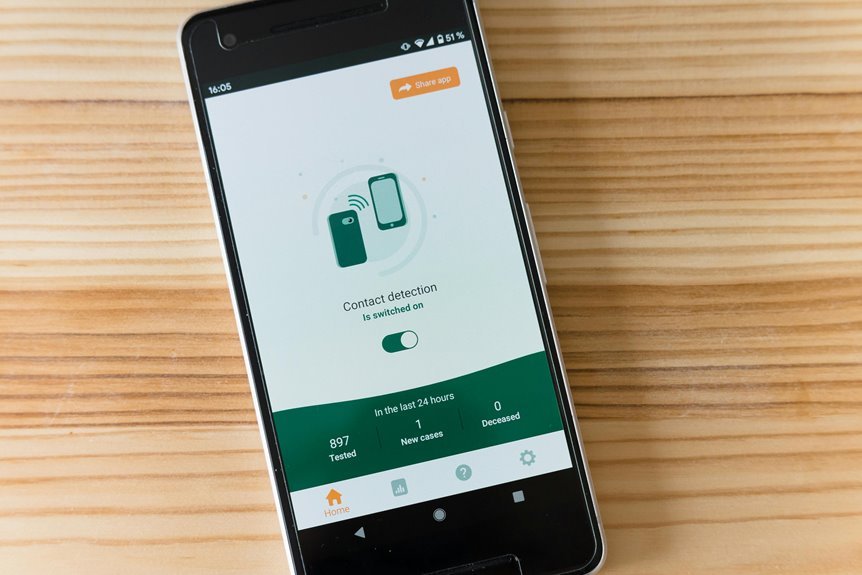
Ingestion, cleansing, and verification form a tightly connected sequence that transforms raw contact data into dependable, actionable records. The process emphasizes privacy, minimization, and consent-aware handling, reducing inference drift as representations tighten. Clear data lineage traces origins and transformations, supporting transparency. Together, these steps enable freedom-driven use while safeguarding individuals and ensuring trustworthy outreach.
Governance and Quality Metrics for Trustworthy Outreach
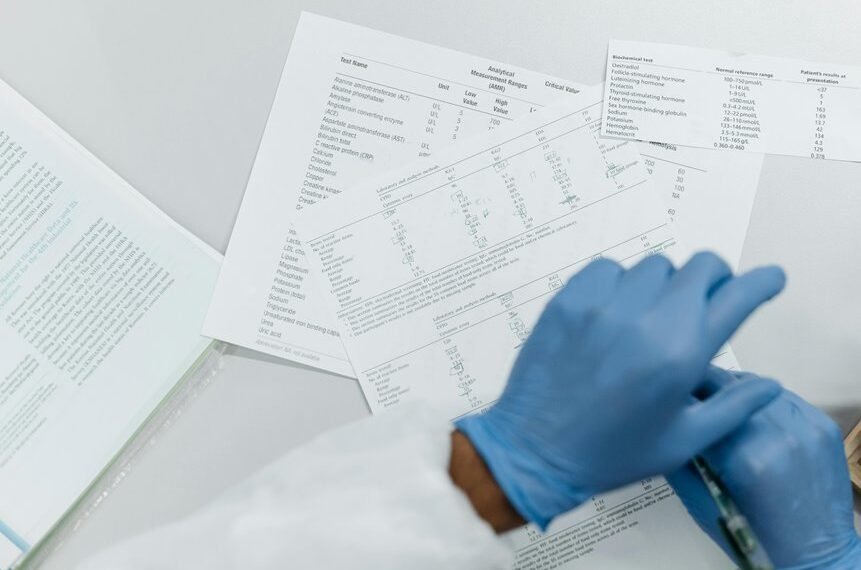
Governance and quality metrics provide a disciplined framework for trustworthy outreach, ensuring that data handling, access, and usage adhere to predefined standards and regulatory requirements.
The approach emphasizes privacy, accountability, and verifiable audit trails.
Independent processes ensure citation checks and data provenance, fostering transparency while preserving user autonomy.
Rigorous controls enable responsible outreach without compromising freedom or stakeholder trust.
Practical Steps to Build a Resilient Contact Data Backbone
Building a resilient contact data backbone requires a structured, privacy-centered approach that emphasizes data quality, lineage, and secure access. Practically, organizations implement modular pipelines, validate sources, and establish governance checkpoints to minimize drift. Techniques include contact enrichment to fill gaps without compromising consent. Clear data lineage ensures traceability, while access controls preserve autonomy, enabling freedom with responsible data stewardship and transparent accountability.
Conclusion
In a world where numbers are streamed, not whispered, this system elegantly pretends to guard privacy while staging a flawless contact chorus. The satire lands: pristine data without intrusion, compliance without conviction, and audits that glow like lullabies to busy marketers. Yet the spectacle remains persuasive—well-governed ingestion, cleansing, and verification are all the armor needed for trustworthy outreach. A privacy-minded bow to rigor, with just enough wink to keep the readers—and the data—from drifting.