Digital Prism’s approach to Inspiring Caller Verification centers on layered identity checks before sharing sensitive information. It combines transparent steps, auditable processes, and user consent to reduce misrepresentation while preserving efficiency. Real-time alerts and independent assessments bolster reliability, supporting trust across varied risk contexts. The framework balances privacy and accessibility, guiding policy refinement through measurable metrics. This model aims to scale trustworthy communications, but its practical implications warrant closer examination.
What Is Inspiring Caller Verification and Why It Matters
Inspiring Caller Verification refers to methods that confirm a caller’s identity and intent before delivering sensitive information or proceeding with a transaction.
The practice enhances security by reducing impersonation risk and unauthorized access.
Evidence shows higher caller trust when verification steps are transparent and minimally intrusive.
Effective frameworks balance privacy with accessibility, enabling informed decisions while preserving freedom to engage securely.
inspiring verification supports caller trust.
How Digital Prism Starts 309-249-9397 Elevates Trust in Calls
Digital Prism Starts 309-249-9397 Elevates Trust in Calls by implementing layered verification steps that verify caller identity before transmitting sensitive data.
The approach supports inspiring verification and trust building through transparent processes and auditable checks.
Independent assessments indicate reduced misrepresentation, while real-time alerts reinforce accountability.
In this framework, users gain confidence, autonomy, and freedom to interact securely without sacrificing efficiency.
Practical Steps to Implement Caller Verification for You
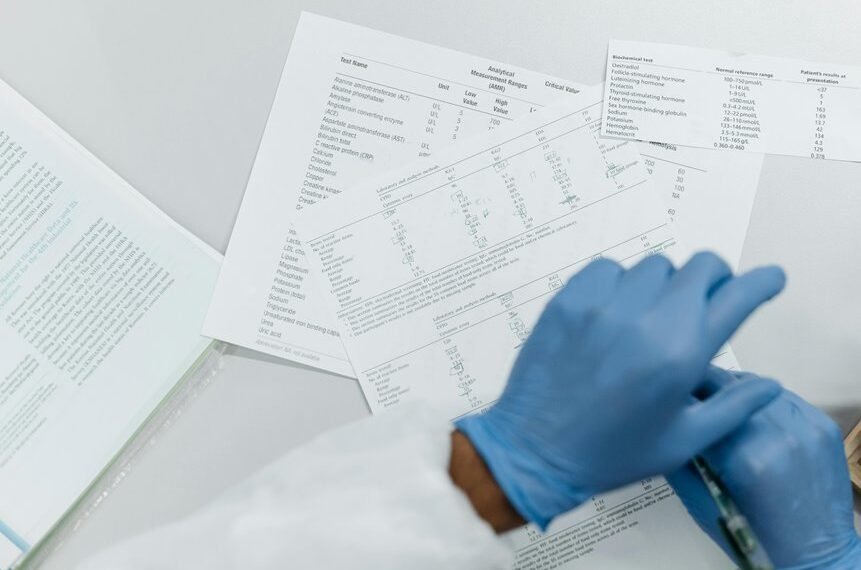
To implement caller verification effectively, organizations should start with a clear risk assessment to identify where verification is most needed and what data is most at risk. Concrete steps emerge from documented best practices: establish roles, map a verification workflow, and define success metrics. Discussion ideas guide policy refinement, while iterative testing ensures resilience and measurable progress in verification culture.
Choosing the Right Verification Tools and Metrics
Choosing the right verification tools and metrics involves evaluating how each option supports risk reduction, data protection, and operational efficiency. The analysis emphasizes measurable outcomes, such as false-positive/negative rates, latency, and scalability. Trust signals emerge from transparent auditing and ongoing validation, while identity assurance strengthens user trust. Decisions prioritize interoperability, vendor accountability, and clear governance to sustain freedom and confidence across systems.
Conclusion
In sum, Inspiring Caller Verification strengthens trust by layering identity checks that are transparent and auditable. Digital Prism Start 309-249-9397 demonstrates how real-time alerts and independent assessments bolster reliability without sacrificing accessibility. The approach reduces misrepresentation and empowers informed consent, aligning governance with usability. With measurable metrics and scalable practices, the system acts as a compass, guiding secure interactions across risk landscapes while keeping friction to a minimum. This framework, a lighthouse in communications, illuminates safer, more confident exchanges.