Radiant Node Start represents the initial activation that enables secure participation in real-time proximity networks. The process establishes device identity, cryptographic keys, and trusted channels to support scalable, privacy-preserving data collection. It balances reproducible analytics with data minimization and auditable governance. This foundation informs exposure inference and accountability mechanisms. The practical implications hinge on secure onboarding and fault-tolerant operation, inviting further scrutiny of implementation details and governance frameworks.
What Radiant Node Start Is and Why It Matters
Radiant Node Start refers to the initial configuration and activation process of a Radiant Node within a distributed contact-tracing or sensing network. The procedure establishes device identity, secure keys, and communication channels, enabling consistent participation. It supports contact tracing workflows and real time analytics, ensuring reproducible data collection, fault tolerance, and scalable deployment for freedom-seeking environments and data-driven decision making.
How Real-Time Contact Tracking Works Under the Hood
Real-time contact tracking operates by continuously exchanging anonymized proximity data between devices, aggregating encounters into time-stamped records, and applying deterministic rules to infer potential exposures.
The system relies on cryptographic tokens and ephemeral identifiers, preserving privacy while enabling cross-device collision detection.
Data minimization and privacy preserving techniques limit collected metadata, reducing risk, while maintaining traceability for public health insights and accountability.
Privacy-First Practices and Security That Build Trust
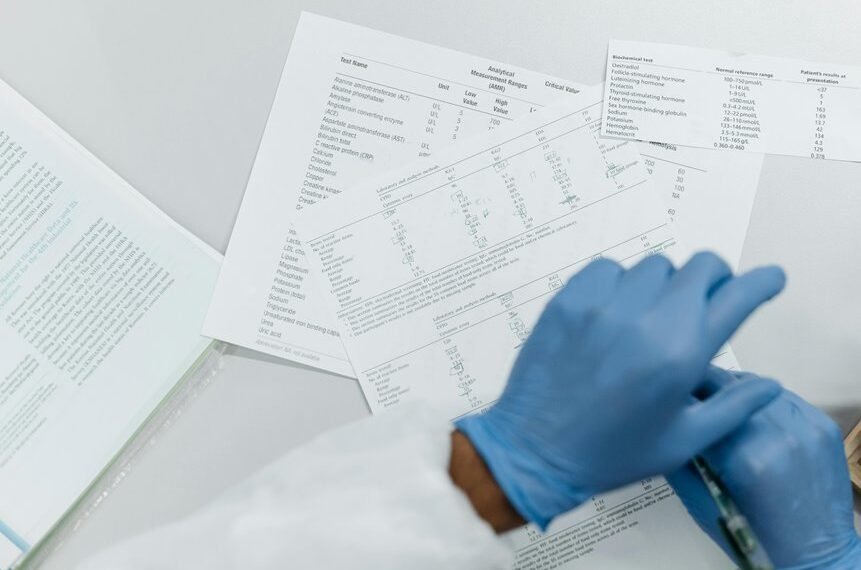
A privacy-first approach emphasizes principled data minimization, robust cryptographic safeguards, and transparent governance to sustain user trust. The analysis presents metrics on privacy first practices, detailing data minimization scopes, retention windows, and access controls. Security by design principles guide system architecture, while explicit user consent mechanisms enable informed participation. Detected risks are quantified, and mitigations prioritize user autonomy and auditable accountability.
Practical Use Cases and Next Steps for Implementation
What concrete use cases most effectively demonstrate the system’s privacy-first design, and what steps are required to implement them at scale?
The evaluation identifies Idea One, Subtopic A; Idea Two, Subtopic B as core pilots, detailing metric-led deployment, risk controls, and governance.
Implementation steps: standardized data minimization, modular pipelines, audits, and scalable onboarding for freedom-focused institutions.
Conclusion
Radiant Node Start is a foundational process that securely initializes devices for real-time proximity networks, enabling reproducible data collection and scalable deployments. By bootstrapping identity, keys, and channels, it ensures fault tolerance, auditable accountability, and privacy-preserving analytics. An anticipated objection—privacy concerns—can be addressed through cryptographic safeguards and data minimization baked into the protocol, guaranteeing that exposure inferences are accurate yet privacy-respecting. In practice, disciplined onboarding and governance validate trusted, scalable, and interoperable implementations.