Radiant Node Start 267-525-9887 unlocks contact information by initiating a decentralized, self-healing data map for real-time routing and synchronization. The process emphasizes provenance, consent, and auditable access, verifying legitimacy through official registries and recent activity. It outlines governance and privacy safeguards to ensure integrity while enabling efficient retrieval. The framework invites scrutiny of verification standards and governance mechanisms, hinting at challenges ahead and the need for careful implementation as systems scale.
What “Radiant Node Start” Means for Contact Data
What does “Radiant Node Start” signify for contact data?
The phrase marks initialization of a distributed contact data map, where a Radiant node initiates data routing, indexing, and synchronization.
It emphasizes decentralized access, resilience, and real-time updates.
The term constrains scope to contact data integrity, availability, and efficient retrieval within a self-healing network.
Radiant node supports streamlined, reliable contact data handling.
How to Verify the Legitimacy of a Phone Number 267-525-9887
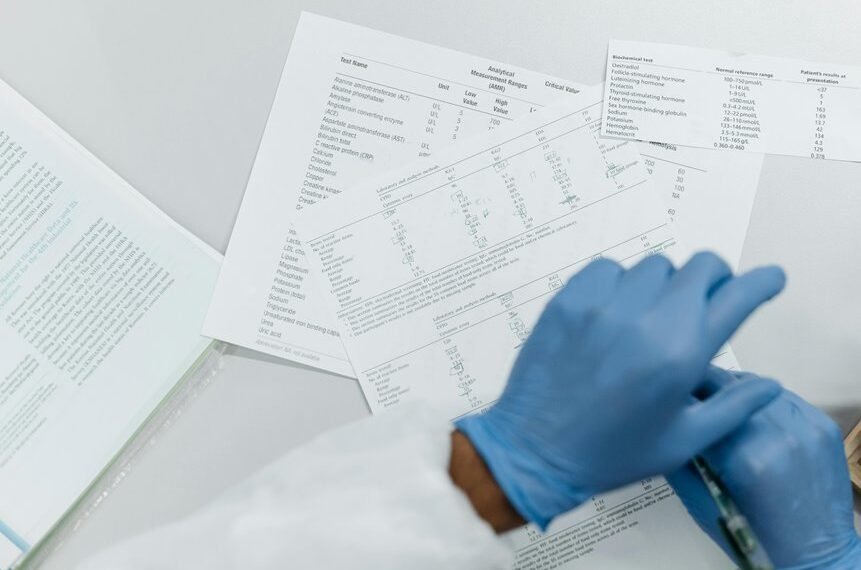
To verify the legitimacy of the phone number 267-525-9887, practitioners should cross-check its assignment with official registries, confirm its carrier and line type, and assess recent call activity for anomalies.
Verification legitimacy emerges through structured checks, verifiable sources, and disciplined practices in contact data management, ensuring accurate records, traceable provenance, and reduced exposure to fraudulent or misattributed contact information.
Best Practices for Ethical Data Use and Consent
Ethical data use and consent considerations build on verified contact information by establishing clear boundaries for collection, storage, and usage. The approach emphasizes autonomy, transparency, and accountability, aligning practices with privacy ethics and proportional data handling.
Organizations should document purposes, obtain informed consent where appropriate, and apply consent best practices to minimize risk while preserving user freedom and trust.
Practical Steps to Protect, Normalize, and Manage Contact Info
Effective protection, normalization, and management of contact information require a systematic, repeatable approach that minimizes risk while preserving data utility. The approach emphasizes privacy practices, clear consent awareness, and robust data ethics. Implement standardized contact verification, minimize unnecessary collection, and maintain auditable access controls. Regular audits detect deviations, while transparent policies empower users to manage consent and update preferences confidently.
Conclusion
The launch of Radiant Node Start for 267-525-9887 unfurls like a quiet lighthouse, its beacon slicing through data fog. Verified provenance shines along crystalline rails, guiding each contact toward transparent, consent-based pursuit. As networks breathe, footprints align, and anomalies dissolve into orderly tides. In this controlled harbor, privacy stands vigilant, governance keeps time, and every retrieval mirrors a clear window—bright, accessible, and trustworthy—for those navigating the map of interconnected lives.